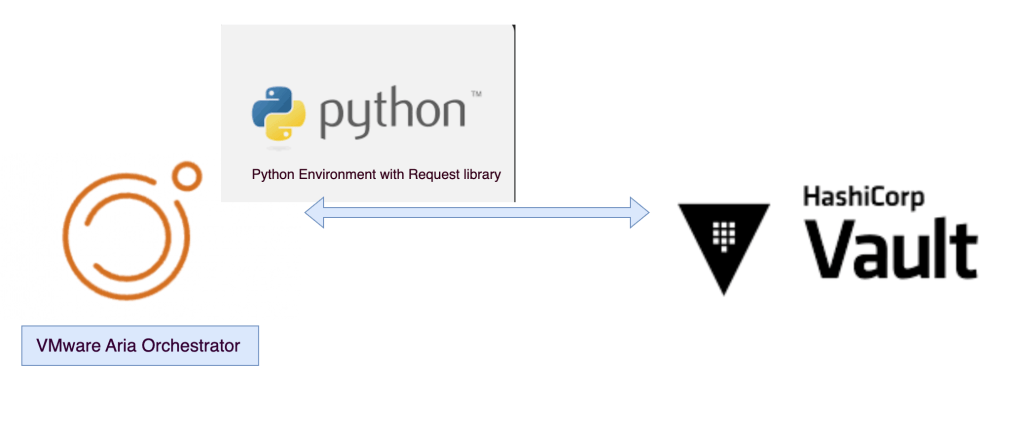
Recently I have come across a used case where we would want to use the secret saved in Hashicorp Vault within vRO workflow .
Business used case is : At the time of rotation of password/secrets , it makes tedious task to rotate the password/secrets in multiple places like secrets in Aria Automation secret or ABX secret or configuration elements etc.
To make it easy , I have come up with python workflow which will pull the details directly from vault from specified folder.
To make this work we need 4 things.
- Vault Service Account Username
- Vault Service Account Password
- Vault foldername path
- Vault Key
Login to VMW Aria Orchestrator aka vRO and Go to Action and click new Action on your desire Module.
import requests
import json
from requests.packages.urllib3.exceptions import InsecureRequestWarning
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
def handler(context, inputs):
class Vault:
def __init__(self, username, password):
self.password = password
self.url = 'https://vault.vmwarecode.com:8200'
self.username = username
def get_token(self):
url = f'{self.url}/v1/auth/ldap/login/{self.username}'
payload = {
"password": self.password
}
headers = {
'accept': "application/json",
'content-type': "application/json"
}
output = requests.post(url, verify=False, data=json.dumps(payload), headers=headers)
if output.status_code == 200:
if output.json():
token = output.json()['auth']
return token['client_token']
else:
raise Exception(f'API result is : {output.status_code} , '
f'More details about Auth api error : {output.json()}')
def list_secret(self, path, vault_key):
url = f'{self.url}/v1/secret/{path}'
header = {
"X-Vault-Token": self.get_token(),
'accept': "application/json",
'content-type': "application/json"
}
output = requests.get(url=url, headers=header, verify=False)
if output.status_code == 200:
if output.json():
if vault_key in output.json()['data'].keys():
return output.json()['data'][vault_key]
else:
raise Exception(f'Specified key does not exist in folder, '
f'Please specify the correct key '
f'here are the list of key available in specified folder \n '
f'{list(output.json()["data"].keys())} ')
else:
raise Exception(f'API result is : {output.status_code} , '
f'More details about Auth api error : {output.json()}')
svc_username = inputs['svc_username']
svc_password = inputs['svc_password']
vault_folder_name = inputs['vault_folder_name']
vault_key_name = inputs['vault_key_name']
vmw = Vault(username=svc_username ,password=svc_password)
vault_secret =vmw.list_secret(path=vault_folder_name, vault_key=vault_key_name)
return vault_secret

Note: I am using Python Environment feature where I have all the packages downloaded already , if you want to know more about Environment check this article .
Line number 10 in code indicates the vault server , Replace the vault with your Vault server .
If you have followed the blog till here , you can run the action and pull details from Vault directly .
One response to “VMware Aria Orchestrator : How to pull Hashicorp Vault secrets using Python action”
hi awesome blog thank u it helped alot .. we are trying to autoamte tkg using the vra and we want to manage the secrets with vault.. but i was wondering if you can install env for request why not use hvac?
LikeLike